February 2009 Vol. 236 No. 2
Features
Global State Of Energy Industry Information Security
With oil prices hovering near $40 a barrel in January 2009, the temptation will exist for energy companies to cut spending. One of the first areas that is likely to be impacted by spending cuts is technology, and, by extension, efforts to bolster information security are at risk. Security issues continue to be of prime importance and should not be sacrificed in light of lower oil prices.
As a matter of fact, security and privacy issues are becoming ever more critical and important in the business world as the Internet continues to emerge as the primary tool for sharing information – both within an organization and to the public at large. Moreover, the prevalence of laptops and other mobile devices in the business world guarantees that critical data is likely distributed across many locations and accessed by many people, making the need for a robust security and privacy strategy a number one priority for companies today. The energy sector is not immune to this need.
Recently, PricewaterhouseCoopers in partnership with CIO Magazine, surveyed a number of CIOs and other executives across a variety of industries, including the energy sector, to determine their approach to privacy and security issues.
In addition to collecting data from energy industry executives about their approach to privacy and security, PricewaterhouseCoopers and CIO Magazine offer recommendations to companies to help improve and address security and privacy needs in 2009 and beyond.
The energy respondents represent a broad geographical spectrum, with participants from North America, South America, Asia, Europe, Africa and the Middle East. Forty percent reported revenues of greater than US$1B.
High-Level Findings
Buoyed by high prices prior to the recent fall of oil prices, and the unprecedented levels of demand and new supplies coming on stream for many commodities, energy executives enjoy improved results across a range of key performance indicators for the industry. While improvements in profitability mask substantial increases in operating costs, it’s clear that one crucial cost center – advancing security and privacy capabilities – has been a strong sector priority for the last couple of years.
Last year, the survey noted progress was made in creating and filling the security chief’s position. This year’s results reflect the kinds of strategic advances that companies make when knowledgeable security leadership is firmly in place. Energy respondents report major gains, for example, in implementing an overall security strategy (67% vs. 59% in 2007), actively monitoring information security intelligence (59% vs. 46%), and investing in the capabilities that build employee security awareness – such as training programs (58% vs. 41%) and people dedicated to running them (58% vs. 45%).
The survey also notes two other key observations from this year’s results. The first is that when security breaches occur, they hurt. Asked about the business impacts of security incidents, many sector respondents cite financial losses (38%), lawsuits or an increase in legal exposure (33%) and intellectual property theft (29%). We note, however, that these represent only the impacts respondents know about. Our second key observation is that, despite strategic advances in security and privacy, about four in every 10 respondents cannot answer basic questions about the risks to their information.
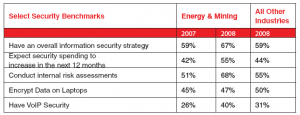
The “select security benchmarks” chart indicates the energy industry is more ahead of the curve than other industries, but work still needs to be done.
Know Where Deficiencies Lie
Signs of maturity: Is a “culture of compliance” taking root and has regulatory compliance declined a bit as a driver of information security spending? Yes, according to sector respondents, who cite it as a key driver less often this year than last (61% vs. 70%) – and are now just as likely to reference compliance with internal policies (62% vs. 55%).
It’s tempting to see this as another sign that compliance is now more deeply embedded within the organization – a view supported by the fact that the sectors are far more likely than the cross-industry average to ensure that information security policies address compliance with legal and regulatory requirements (60% vs. 41%). Other responses, though, suggest that sector executives may not have a full picture of compliance lapses: only 55% audit and monitor user compliance with security policies and a little less than half conduct compliance testing (49%).
Privacy protection: Most energy companies aren’t sure exactly where sensitive data is located. If energy companies are internalizing compliance practices, the trend isn’t yet evident in their ability to protect the privacy of customer and employee information. Although doing so requires knowing first where this sensitive data resides, only 35% of energy respondents report that they have an accurate inventory of where personal data for customers and employees is collected, transmitted, and stored. More than half (51%) could begin lowering risk immediately – by implementing some low-cost privacy protections such as requiring employees to certify in writing that they are complying with the company’s privacy policies.
Intellectual property and other critical data: Opportunities to advance key safeguards abound. Also at risk are vast quantities of other important data – such as proprietary exploration and production details, geophysical data and plant security designs. On the one hand, the sector’s responses reveal that last year’s focus on encrypting data in laptops has extended to encrypting data in other media – such as databases (55% vs. 41%), file shares (50% vs. 32%), backup tapes (55% vs. 37%), and removable media (45% vs. 25%). But many sector respondents say their company’s information security policies do not address data protection, disclosure and destruction (41%) or classifying the business value of data (66%).
Third-party security: trust isn’t a strategy. Both capitalizing on new opportunities and ensuring cost-effective operations depend on sharing information with others. Only a minority of sector respondents, however, say their firm conducts security – and privacy-related due diligence of third parties handling customer or employee information (27%), and even fewer have an inventory of these parties at hand (25%). This is a crucial issue because, as regulators have made clear, companies must, in essence, keep focused on safeguarding data even when it is shared with third-party service providers. Steps to take in the coming year:
1. Get the right people together. If a Chief Information Security Office (CISO) position hasn’t been established, consider doing so. Then work to actively engage both business and IT decision-makers in addressing security; today, almost half do not (45%). Also, take a closer look at the positive security benefits that accrue to the 20% of competitors that employ a Chief Privacy Officer (CPO). While not required by most regulations, designating a CPO demonstrates to regulators a serious commitment to privacy protection and can help lower risks by having one executive focused on helping “connect the dots.”
2. Improve identity management. Controlling access is essential. Although energy sector respondents report advances in deploying centralized user data stores (68% vs. 50%), most say their company has yet to implement systems in many areas – such as reduced/single sign-on software (44%) and automated account deprovisioning (32%).
3. Focus more intensely upon critical security processes. During 2008, the sector has made enormous advances in implementing technical systems, such as content filters (83% vs. 54%), intrusion prevention tools (72% vs. 53%), and tools to discover unauthorized devices (54% vs. 39%). But getting the most value from this technology will require better support from critical processes. Yet, in significant numbers, energy respondents say their organization has not implemented an identity management strategy (53%), integrated security with privacy/compliance plans (63%), or established a business continuity or disaster recovery plan (37%).
4. Strengthen incident response planning. When a security breach occurs, taking the right steps can prevent major impact to business and brand integrity, protect evidence, and help reinforce relationships with customers and regulators. Many competitor companies are not: 47% of sector respondents say their organization’s security policies do not address incident response and only 30% have an incident response process to address breaches involving third parties handling data.
What should be done? Take a top-down approach. First, ensure a strategic, integrated and holistic approach to incident response staffed by an inter-disciplinary team. Second, plan a consistent set of response procedures for different incidents – including those affecting security, privacy and compliance issues. Then, review security and privacy policies and practices and align them with incident-response positioning. And lastly, test the program.
In short, many strides have been made to improve security and privacy issues in the energy sector, but certainly more can be done. A solid plan and solid approach today can save significant time, money and resources tomorrow.
Author
Ray Slocumb is the Houston Office leader for the Advisory practice of PricewaterhouseCoopers. In this capacity he manages over 150 professionals with varying backgrounds and skills related to business and systems consulting. His role includes managing various types of engagements including those related to project management, process improvement, systems integration, systems strategy, ERP consulting and controls, data warehousing, IT Internal Audit, risk management, business process, security and technology services. He also frequently coordinates global PricewaterhouseCoopers resources for multinational clients. Ray is a Certified Information Systems Auditor (CISA) and a Certified Fraud Examiner (CFE). Email: raymond.e.slocumb@us.pwc.com.


Comments